What is Authentication?
Authentication before allowing access to a network or its resources, is the act of verifying the identity of a user, device, or system by validating specified credentials. It stops systems from being used without authorization and guarantees safe communication in a network setting.
Authentication Techniques
Depending on the kind of credentials being used, many techniques can be utilized to accomplish authentication. The commonly used techniques are:
- Authentication Using Passwords
The most popular technique of authenticating. Unique username and password is given to each user. At login, when the password is entered that is compared to the saved password, which is encrypted. Access is allowed only if the credentials match otherwise it denies. Password strength and security against phishing and guessing attempts are key components of security. - Physical Identification
It makes use of tangible items like smart cards, tokens, badges, and ID cards and then in order to verify the user, the system confirms that the physical item is in their sight. Also, frequently used when combined with PINs or passwords to boost security. More use in offices, ATMs, and places with restricted access.
A security risk may arise if the card is lost or stolen. - Verification via Biometrics
It depends on each person’s distinct biological or behaviors traits. Also, this type of technique removes the need to carry physical tokens or remember passwords. Considered as higher security because it is hard to duplicate but also needs precise data collection and specialized hardware.
Types of Authentication
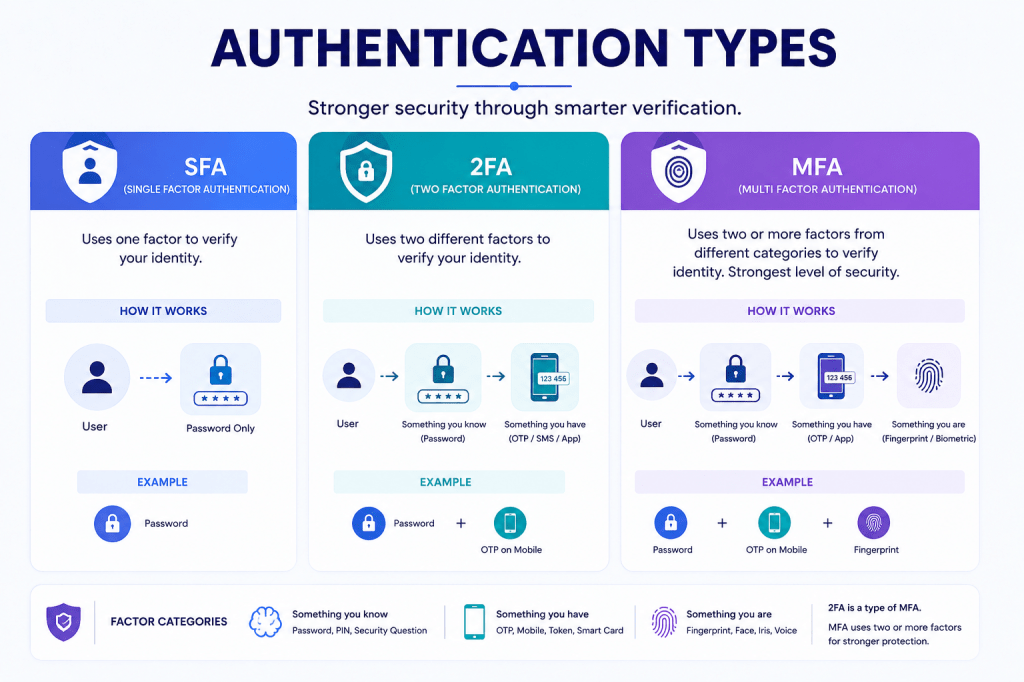
- Single-Factor Authentication(SFA)
A username and password are basically the only methods of verification used in single-factor authentication. When the entered information matches the recorded value, the system allows access. It is mostly used in systems where good security is not as important as ease of access. Password strength and user behavior are the only factors that affect security in this type. - Two-Factor Authentication(2FA)
To verify identification, two distinct authentication aspects are needed for two-factor authentication. It usually combines the user’s holdings (OTP, token, smart card) with their credentials (password). The second aspects help in preventing unwanted access even in the event that one is compromised. It is mostly utilized in workplace systems, email services, and online banking. - Multi-factor authentication(MFA)
Multi Factor Authentication verifies an individual’s identification using two or more independent factors such as passwords, physical items, and biometric characteristics might all be combined. It is used for institutions where security and data sensitivity are at priority and offers multi-layered security against complicated cyberattacks.
Applications
- Banking & Financial Systems: PINs, OTPs and biometric authentication are used to secure ATMs, mobile banking, and internet transactions.
- Enterprise and Organizational Systems: Manages access to private organizational resources, internal servers, and applications.
- Network Access Control: Limits authorized users and devices access to both private and business networks.
- Email and cloud services: Use multi-factor and password-based authentication to safeguard private user information.
Conclusion
Authentication is very important to prevent unwanted access to networks, systems and sensitive data. It guarantees safe use of digital resources and secure communication by confirming the identity of people, devices, or systems. In order to preserve data privacy and system security, authentication has become crucial in banking, organizations, cloud services, and control of network access due to the growing usage of online services.
FAQs
- What does networking authentication mean?
Authentication, before granting access to a network or its resources is the process of confirming the identity of a user, device or system.
- What is the one main difference between MFA from 2FA?
MFA includes two or more independent factors for great security, such as passwords, OTPs, smart cards or biometrics, whereas 2FA uses two verification factors.
- What biometric authentication situations are there?
Typical biometric authentication technique include voice recognition, facial recognition, iris scanning and fingerprint scanning.